
Introduction
VoIP is now the backbone of modern business communication—and as more calls move from copper circuits to IP networks, they've become targets for fraud, interception, and increasingly sophisticated abuse. Heading into 2026, VoIP attacks are growing in both volume and technical complexity. Telecom fraud losses reached $41.82 billion globally in 2025, and new threats like AI-powered voice cloning are rewriting the rules of trust.
This guide walks you through the key threats every VoIP user faces, business or personal, and delivers actionable defenses: network-level protections, provider vetting criteria, and configuration best practices. You'll leave with a concrete security plan you can act on.
TLDR: Key VoIP Security Takeaways
- VoIP calls are vulnerable to interception and fraud when transmitted without encryption
- Top threats include toll fraud, AI-powered vishing, and automated SIP scanning targeting weak credentials
- SRTP + SIP-TLS encryption and strong authentication form your security foundation
- Your provider's built-in safeguards matter too: robocall blocking, two-factor authentication, and virtual number privacy all reduce your exposure
Why VoIP Security Deserves More Attention in 2026
The Shift from PSTN to IP
Traditional phone calls ran over dedicated copper circuits—physically isolated pathways that were inherently difficult to tap at scale. VoIP voice data packets travel across shared IP networks, exposing them to the same attack surface as any internet-connected service. This architectural shift means VoIP systems face the same threats as web servers and cloud infrastructure—just routed through your phone system.
What's New in 2026
AI-generated voice cloning has moved from proof-of-concept to active threat. The FBI documented over $893 million in AI-enabled fraud losses in 2025, with Business Email Compromise scams increasingly incorporating AI voice cloning.
In one high-profile case, attackers used deepfake video and audio to trick a finance worker at Arup into transferring $25.6 million. Executives and customers can now be impersonated convincingly with just seconds of recorded audio.
Automated attack toolkits are scanning for exposed SIP endpoints at industrial scale. Research shows 7.4 million SIP scanning requests from 839 IPs in a single year, while Shodan indexes over 3.4 million exposed SIP ports globally. If your SIP server is reachable from the public internet without access controls, it will be found and probed.
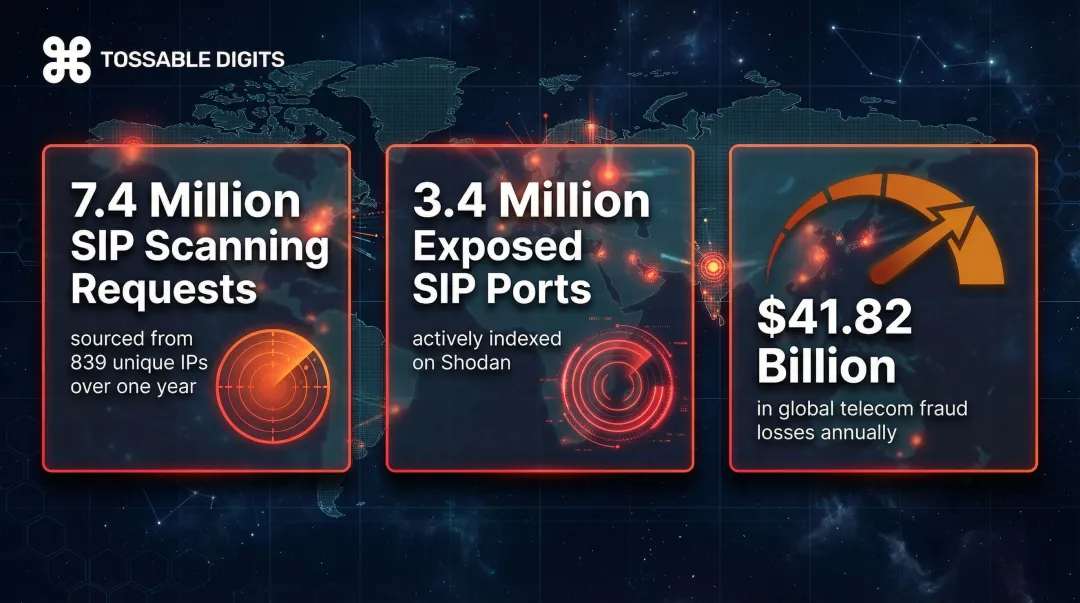
The Cost of Inaction
That exposure has a direct price tag. Global telecom fraud losses hit $41.82 billion in 2025, up nearly $3 billion from 2023. Fraudsters increasingly target enterprise VoIP infrastructure to execute International Revenue Share Fraud (IRSF) and toll fraud, turning corporate voice networks into unauthorized billing engines — sometimes racking up five-figure charges before anyone notices.
The Most Common VoIP Security Threats
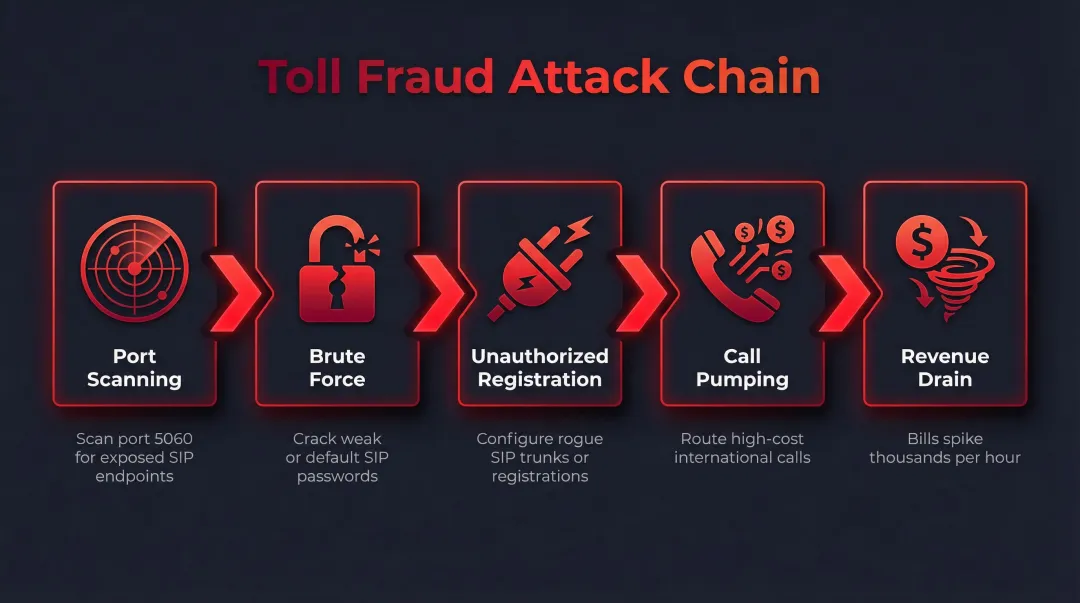
Toll Fraud: The Most Financially Damaging Attack
Toll fraud occurs when attackers scan for misconfigured SIP servers or brute-force weak credentials, then route large volumes of expensive international or premium-rate calls through the compromised system. Losses can reach tens of thousands of dollars before anyone notices — often because attacks run overnight or over weekends when monitoring is minimal.
How it works:
- Attackers use automated tools to scan port 5060 for exposed SIP endpoints
- They brute-force default or weak SIP passwords (admin/admin, 1234, extension number, etc.)
- Once inside, they configure unauthorized SIP registrations or trunk routes
- They pump high-cost international calls—often to revenue-share destinations where the attacker splits profits with fraudulent carriers
- Bills spike rapidly, sometimes thousands of dollars per hour
Eavesdropping and Call Interception
Unencrypted VoIP traffic transmits voice as standard RTP packets that can be captured with freely available packet-sniffing tools like Wireshark. This is especially dangerous on public Wi-Fi or poorly segmented office networks.
What's at stake:
- Legal conversations protected by attorney-client privilege
- Financial details including account numbers and transaction data
- Healthcare discussions containing protected health information (PHI)
- Competitive business strategy and M&A discussions
- Authentication credentials spoken during support calls
SIP Registration Hijacking
SIP hijacking occurs when attackers steal or brute-force SIP credentials to register their own device under a legitimate user's account. Once registered, the attacker controls that extension — redirecting incoming calls, placing outbound calls on your bill, or harvesting voicemail for sensitive data.
Weak or default SIP passwords are the primary enabler. Key risk factors include:
- IP phones shipped with predictable factory credentials
- IT teams skipping credential changes during rushed deployments
- Extensions using the extension number itself as the SIP password
Denial-of-Service and Call Flooding
Flooding a VoIP server with fake INVITE or REGISTER requests exhausts system resources and knocks out call service—critical for businesses that depend on phone availability for sales, support, or emergency operations. VoIP-targeted DoS differs from generic network DDoS because it exploits protocol-specific behaviors in SIP processing, requiring VoIP-aware mitigation.
Vishing and AI-Powered Voice Fraud
Vishing (voice phishing) is social engineering conducted via phone—attackers impersonate IT support, banks, or executives to extract credentials or authorize transfers.
AI voice cloning has raised the stakes considerably. These tools now generate convincing real-time impersonations from just a few seconds of audio scraped from YouTube, LinkedIn videos, or earnings calls. Caller ID-based trust is no longer reliable — an employee can receive what sounds exactly like their CFO's voice requesting an urgent wire transfer, with no technical signal that the audio is synthetic.
VoIP Security Best Practices
Strong Authentication and Password Hygiene
Default SIP credentials must be changed immediately on every device and account. Enforce complex, unique passwords for each extension—minimum 12 characters combining uppercase, lowercase, numbers, and symbols. Enable multi-factor authentication (MFA) wherever your platform supports it.
Critical: A significant share of VoIP breaches trace back to unchanged default passwords. The Verizon 2024 Data Breach Investigations Report found that 77% of Basic Web Application Attacks used stolen credentials, with 21% using brute force. VoIP systems face the same threat.
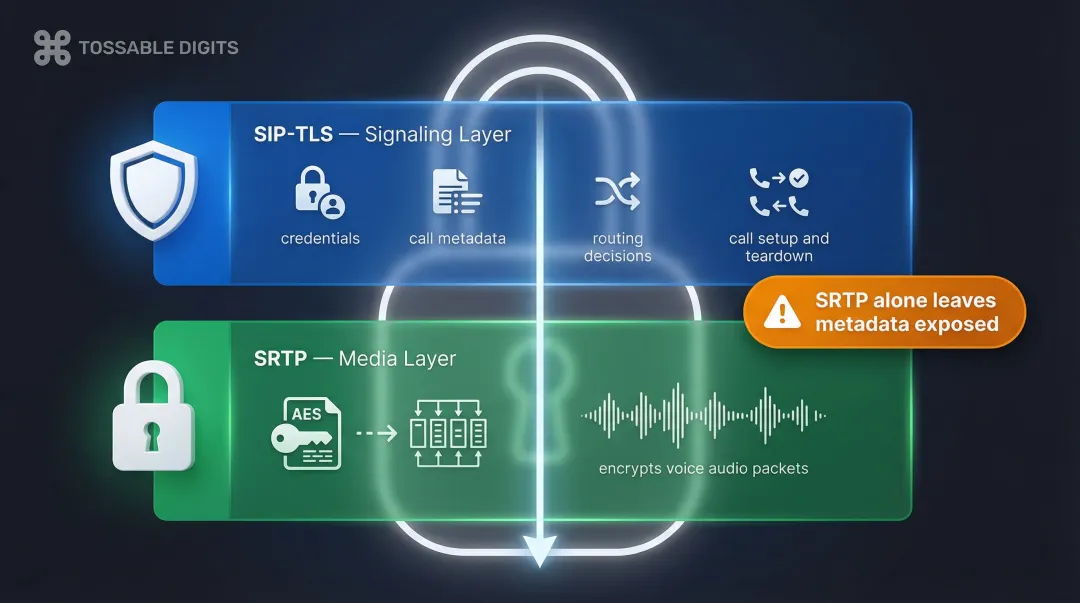
Encrypt All Voice Traffic
VoIP encryption requires two layers:
SIP-TLS secures the call signaling layer (setup, routing, teardown). This protects your SIP credentials, call metadata, and routing decisions from interception. Without SIP-TLS, attackers can see who you're calling, when, and for how long—even if they can't hear the conversation.
SRTP encrypts the actual voice media packets in transit using AES encryption. This prevents eavesdropping on the conversation content itself.
SRTP alone isn't enough — without SIP-TLS, call metadata and SIP credentials remain exposed even if the audio is encrypted.
Keep Firmware and Software Updated
VoIP phones, SIP servers, and softphone applications receive firmware patches that close known vulnerabilities. Unpatched edge devices saw an eight-fold increase in exploitation as initial access vectors in 2025.
Practical update cadence:
- Check for critical patches monthly
- Apply security updates immediately when released
- Subscribe to vendor security bulletins
- Managed or cloud-hosted VoIP typically handles this automatically
Use VPNs for Remote and Mobile Workers
Remote VoIP clients are especially exposed because calls from home networks or public Wi-Fi bypass corporate network controls entirely. Always route remote VoIP traffic through a business VPN.
Important: Split-tunneling configurations should explicitly include VoIP traffic in the encrypted tunnel. Don't exclude SIP ports from the VPN to "improve call quality"—this defeats the entire security purpose.
Protect Your Real Phone Identity with Virtual Numbers
Network-level controls protect your infrastructure — but your phone number itself is also an attack vector. For individuals, small business owners, and professionals fielding calls from unknown parties, publishing a virtual number instead of your direct number adds a concrete privacy layer.
Why this matters:
- Callers never learn your real number, reducing spoofing risk
- You can dispose of compromised numbers without changing your actual phone
- Reduces social engineering exposure—attackers can't use your real number for impersonation
- Limits harassment by providing an isolatable contact point
Tossable Digits includes robocall blocking, number isolation, and voicemail-to-email in every plan. Calls forward to your real phone, but that number stays completely hidden from callers, including in voicemail callbacks and SMS replies.
Securing Your Network for VoIP
VLAN Segmentation for Voice Traffic
Network segmentation places VoIP devices on a dedicated voice VLAN, isolating voice packets from general data traffic. This limits an attacker's ability to pivot from a compromised workstation to the phone system.
Benefits:
- Improved Quality of Service (QoS) by preventing bandwidth conflicts
- Reduced attack surface—compromised PCs can't easily sniff voice traffic
- Easier monitoring and policy enforcement for voice-specific traffic
- Many managed switches support automatic voice VLAN assignment via LLDP-MED
Configure Access Control Lists (ACLs) to restrict inter-VLAN routing, preventing unauthorized access from data networks to VoIP servers. Once your voice traffic is isolated, the next layer of defense sits at the network edge.
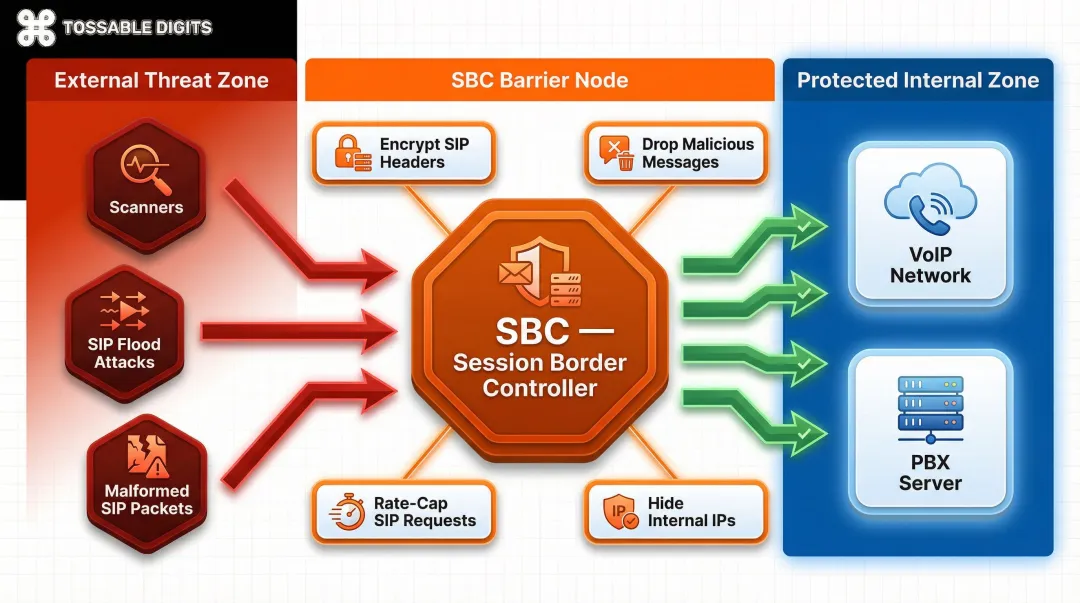
Firewalls and Session Border Controllers
A properly configured firewall filters SIP traffic to allow only known IP ranges, blocking the automated scanning that feeds brute-force attacks. But firewalls alone aren't enough.
Session Border Controllers (SBCs) act as VoIP-aware security proxies at the network edge:
- Encrypt SIP header fields to hide your internal network structure from external parties
- Cap SIP request rates to stop flood attacks before they reach your PBX
- Detect and drop malformed or malicious SIP messages before they cause damage
- Route media streams across network boundaries without exposing internal IP addresses
SBCs are especially critical for businesses with public-facing SIP trunks—they prevent your PBX from being directly reachable on the open internet. Combined with call log monitoring, they give you both perimeter defense and early-warning visibility.
Monitor Call Logs and Set Anomaly Alerts
Real-time monitoring of Call Detail Records (CDRs) can detect toll fraud early, before it racks up catastrophic charges.
Configure alerts for:
- Sudden spikes in international call volume
- Unusual after-hours calling activity
- Calls to high-cost destinations (premium-rate numbers, exotic country codes)
- Extensions making calls they've never made before
- Abnormal call durations or patterns
Set hard caps on international calling for extensions that don't need it—if your sales team only calls North America, block international dialing for those extensions entirely. Locking down unused capabilities is just as important as monitoring active ones.
Disable Unused Features and Restrict Administrative Access
Turn off VoIP features not in active use. If your organization doesn't need international dialing, disable it system-wide. If you don't accept anonymous calls, require caller ID. If you don't use web-based provisioning, disable those admin portals.
Limit administrative access:
- Restrict PBX management console access to specific IP addresses
- Use jump boxes or VPNs for remote administration
- Implement role-based access control—not everyone needs full admin rights
- Log all administrative actions for audit trails
What to Look for in a Secure VoIP Provider
Non-Negotiable Security Baseline
Start with encryption: SRTP/SIP-TLS should be standard, not a premium add-on. Every call should be encrypted by default, not just on higher-tier plans.
Multi-factor authentication (MFA) must be available on both user accounts and the admin console. If 2FA is locked behind an upgrade, that's a red flag worth taking seriously.
Get clarity on uptime and SLA commitments before signing up. Does the provider offer DDoS mitigation? What's their incident response time when something goes wrong?
Built-In Fraud Controls
A reputable provider should offer toll fraud detection as standard—not as a separate add-on you have to ask for. Look for:
- Automated call caps or rate limits you can configure
- Geographic dial-plan restrictions (block entire countries if not needed)
- Robocall and spam call blocking using industry databases and AI detection
- Real-time alerting when unusual calling patterns are detected
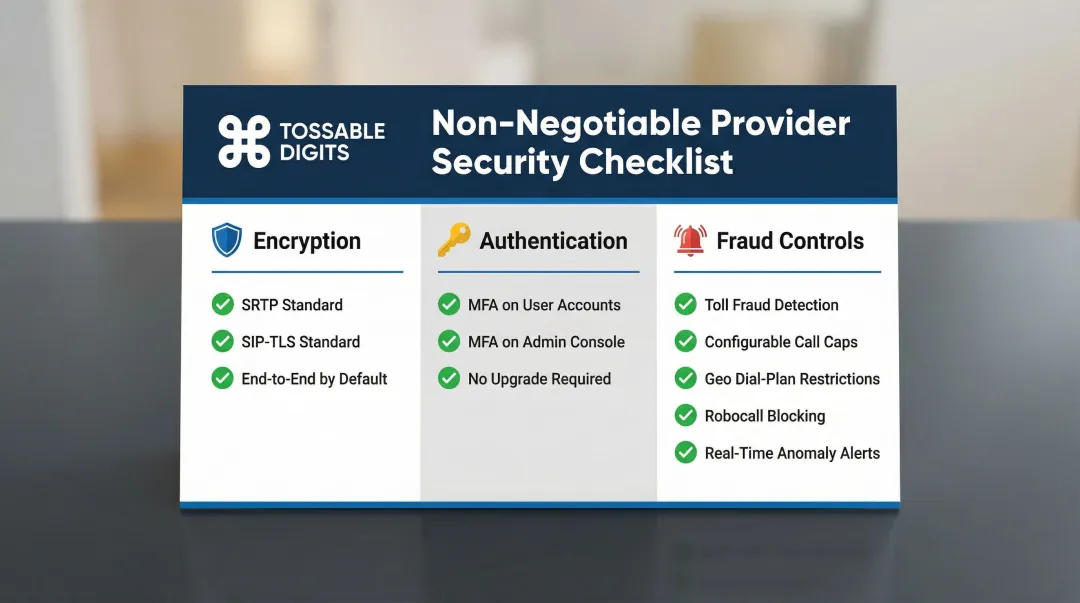
Tossable Digits includes robocall blocking and two-factor authentication across all plans at no additional cost. Check whether your current or prospective provider meets this baseline—or quietly charges extra for it.
Compliance Readiness for Regulated Industries
For businesses in healthcare, legal, or finance, confirm whether the provider's platform supports the encryption and audit-log requirements of HIPAA, PCI-DSS, or relevant data protection laws.
Ask specifically:
- Where are call recordings and voicemail data stored?
- How long is this data retained?
- Who has access to call metadata and recordings?
- Can the provider sign a Business Associate Agreement (BAA) for HIPAA compliance?
- Does the platform support the "strong cryptography" requirement in PCI-DSS for cardholder data transmitted over VoIP?
Frequently Asked Questions
Is VoIP secure enough for business use?
Modern VoIP is highly secure when properly configured. SRTP and SIP-TLS encryption, combined with strong authentication and network segmentation, deliver business-grade protection. Misconfiguration and weak credentials are where most real-world breaches originate.
What is the most common VoIP security threat?
Toll fraud is the most financially damaging and prevalent attack. Attackers compromise SIP credentials through brute-force or default passwords, then route expensive international calls through the victim's system. Prevention requires strong passwords, MFA, and real-time CDR monitoring.
Can VoIP calls be intercepted or hacked?
Unencrypted VoIP calls can be captured on the same network using basic packet-sniffing tools. SRTP and SIP-TLS encryption make interception of properly secured calls extremely difficult in practice — the same protection level your browser uses for secure websites.
What is SIP-TLS and how is it different from SRTP?
SIP-TLS encrypts the call signaling layer—the setup, routing, and teardown messages that establish calls. SRTP encrypts the audio media packets that carry your voice. Together, they provide full end-to-end protection of both content and metadata.
How do virtual phone numbers improve security and privacy?
Virtual numbers shield your real phone number from public exposure, reducing spoofing risk and social engineering attacks. Callers never learn your actual contact information, limiting harassment and preventing attackers from using your real number for impersonation campaigns.
Do remote workers face higher VoIP security risks?
Yes. Remote VoIP clients on home or public networks bypass corporate security controls entirely, exposing calls to interception and devices to compromise. VPN use and strong device authentication are essential for distributed teams making business calls from untrusted networks.


